Определить, на какой стадии алкогольной зависимости находится человек, важно как для выбора методов лечения,
Самостоятельная обработка может лишь сократить численность паразитов. На первый взгляд даже может показаться, что
Диваны "Еврокнижка" с ортопедическим матрасом представляют собой идеальное сочетание функциональности и комфорта для современного
Реабилитация алкоголиков является ключевым этапом на пути к выздоровлению и возвращению к полноценной жизни.
Развитие технологий в аппаратной косметологии продолжает набирать обороты, обещая еще больше инновационных решений в
Современные клиники в Китае оснащены передовым оборудованием и применяют инновационные методики лечения, что позволяет
Столовые сервизы не просто функциональный элемент стола, но и важная деталь, придающая особенный шарм
В эру цифровых технологий социальные сети стали мощным инструментом для продвижения личных и коммерческих
Всем известно, что, в принципе, любые столы могут иметь разную форму. Так, есть столы
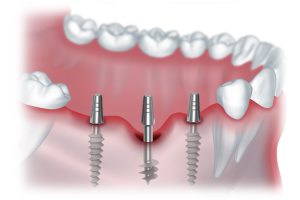
В последнее время в стоматологии наблюдается тенденция к разработке биосовместимых и функциональных материалов.
Сказки играют ключевую роль в развитии ребенка. Они стимулируют воображение, что является важным элементом
Выбор экологически чистых вешалок – это не только практическое решение, но и заявление о
Чай в Иране традиционно заваривается в специальном чайнике, который ставят на кипящий самовар, чтобы
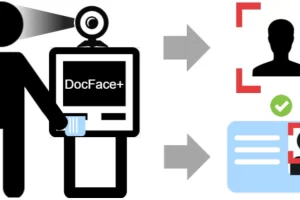
Возможность доступа к различным базам данных предоставляет широкие возможности для сбора и анализа информации
Фотоомоложение IPL (интенсивное импульсное световое облучение) – это метод косметологической процедуры, который использует специальное
Путешествия по России открывают перед туристами уникальную возможность исследовать одну из самых больших и
Подробнее об этом можно узнать на telega.in/blog, где представлены полезные статьи и рекомендации по
Элайнеры – это современное и эффективное решение для исправления прикуса без использования традиционных брекетов.
Организация свадьбы начинается с формирования общего видения торжества. Важно учитывать предпочтения и желания молодоженов,
Аппаратная косметология является одним из наиболее динамично развивающихся направлений в современной индустрии красоты.
Имплантаты позволяют не только восстановить функциональность зубов, но и сохранить естественный внешний вид улыбки.
Современные аппараты для лазерной эпиляции используют передовые технологии, предлагая максимальную эффективность процедуры при минимальном
Женские жилеты являются универсальным элементом гардероба, который подходит как для повседневного, так и для
Тайский массаж спины – это древняя практика, сочетающая в себе элементы аккупрессуры, йоги и
МФО "Бустра" выделяется на рынке быстрыми и удобными условиями получения займов, что делает ее
Бижутерия играет важную роль в создании уникального и выразительного образа. Она доступна в различных
Миома матки - это образование, которое в медицинском мире часто называют "спящей бомбой". Отсутствие
Секреты традиционной восточной медицины уже давно и уверенно пробрались во все уголки мира. Методики
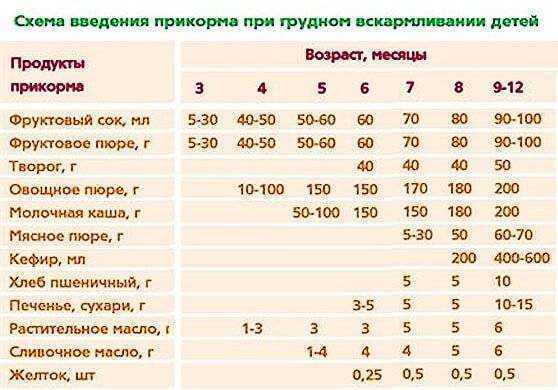
Для правильного развития пищеварительной системы ребенок должен получать твердую пищу. Рассмотрим, как и когда